Day 2 of Network Field Day started out with a super-sized session at the Juniper headquarters. We arrived a bit hungover from the night before at Murphy’s Law and sat down to a wonderful breakfast with Abner Germanow. He brought coffee and oatmeal and all manner of delicious items, as well as Red Bull and Vitamin Water to help flush the evil of Guiness and Bailey’s Irish Cream from our systems. Once we were settled, Abner gave us a brief overview of Juniper as a company. He also talked about Juniper’s support of Network Field Day last year and this year and how much they enjoy having the delegates because we ask public questions and wish to obtain knowledge to make the world a better place for networkers despite any ridicule we might suffer at each other’s hands.
Dan Backman was next up to start things off with an overview of Junos. Rather than digging into the gory details of the underlying operating system like Mike Bushong did last year, Dan instead wanted to focus on the extensibility of Junos via things like XML and API calls. Because Junos was designed from the ground up as a transactional operating system, it has the ability to do some very interesting things in the area of scripting and automation. Because changes made to a device running Junos aren’t actually made until they are committed to the running config, you can have things like error checking scripts running in the background monitoring for things like OSPF processes and BGP neighbor relationships. If I stupidly try to turn off BGP for some reason, the script can stop me from committing my changes. This would be a great way to keep the junior admins from dropping your BGP sessions or OSPF neighbors without thinking. As we kept moving through the CLI of Junos, the delegates were becoming more and more impressed with the capabilities inherent therein. Many times, someone would exclaim that Junos did something that would be very handy for them, such as taking down a branch router link if a keepalive script determined that the remote side had been brought down. By the end of Dan’s presentation, he revealed that he was in fact not running this demo on a live router, but instead had configured everything in a virtual instance running in Junosphere. I’ve written a little about Junosphere before and I think the concept of having a virtual instantiation of Junos that is easily configurable for many different types of network design. Juniper is using Junosphere not just for education, but for customer proof-of-concept as well. For large customers that need to ensure that network changes won’t cause major issues, they can copy the configuration from their existing devices and recreate everything in the cloud to break as they see fit. Only when confirmed configs are generated from the topology will the customer then decide to put that config on their live devices. All this lists for about $5/router per day from any Juniper partner. However, Dan hit us with our Network Field Day “Oprah Moment”. Dan would give us access to Junosphere! All we have to do is email him and he’ll get everything setup. Needless to say, I’m going to be giving him a shout in the near future.
Next up was Dave Ward, Juniper’s CTO of the Platform Divison. A curious fact about Dave: he likes to present sans shoes. This might be disconcerting to some, but having been through business communications class in college, I can honestly say it’s not the weirdest quirk I’ve ever seen. Dave’s presentation focused around programmable network, which is Juniper’s approach to OpenFlow. Dave has the credentials to really delve into the weeds of programmable networking, and to be honest some of what he had to say went right by me. It’s like listening to Ivan turn the nerd meter up to 9 or 10. I recommend you watch part one of the Juniper video and start about halfway through to see what Dave has to say about things. His ideas behind using our new found knowledge of programmable networking to better engineer things like link utilization and steering traffic to specific locations is rather interesting.
Next up was Kevin with a discussion about vGW, which came for Altor Networks, and using Juniper devices to secure virtual flows between switches. This is quickly become a point of contention with customers, especially in the compliance area. If I can’t see the flows going between VMs, how can I certify my network for things like Payment Card Industry (PCI) compliance? Worse yet, if someone nefarious compromises my virtual infrastructure and begins attacking VMs in the same vSwitch, if I can’t see the traffic I’ll never know what’s happening. Juniper is using vGW to address all of these issues in an easy-to-use manner. vGW allows you to do things like attach different security policies to each virtual NIC on a VM and then let the policy follow the VM around the network as it vMotions from here to eternity. vGW can also reroute traffic to a number of different IDS devices to snoop on traffic flows and determine whether or not you’ve got someone in your network that isn’t supposed to be there. There’s even a new antivirus module in the new 5.0 release that can provide AV services to VMs without the need to install a heavy AV client on the host OS and worry about things like updates and scanning. I hope that this becomes the new model for AV security for VMs going forward, as I realize the need to run AV on systems but detest the fact that so many software licenses are required when there is a better solution out there that is quick and easy and lightweight.
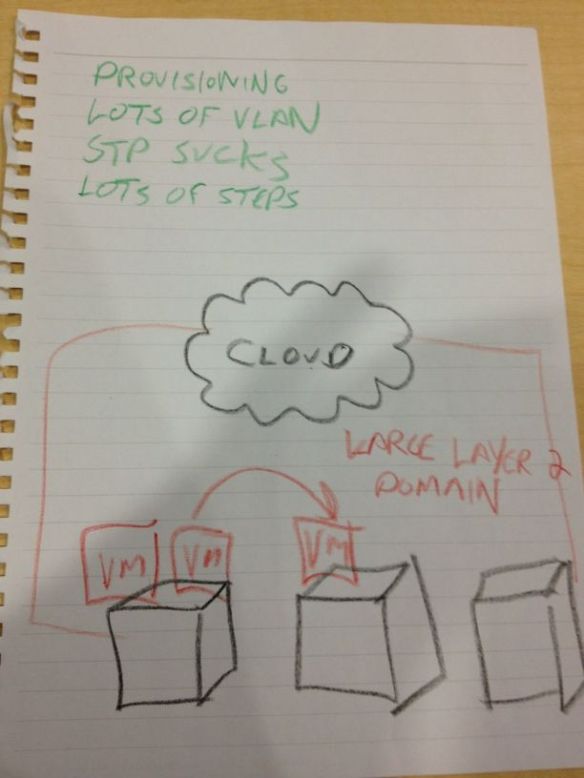
The last presentation was over QFabric. This new technology represents Juniper’s foray in the the fabric switching technology sweeping across the data center like wildfire right now. I’ve discussed at length my thoughts on QFabric before. I still see it as a proprietary solution that works really well for switching packets quickly among end nodes. Of course, to me the real irony is that HP/Procurve spent many years focusing on their Edge-centric network view of the world and eventually bought 3COM/Huawei to compete in the data center core. Juniper instead went to the edge-centric model and seems to be ready to bring it to the masses. Irony indeed. I do have to call out Juniper here for their expected slide about “The Problem”:
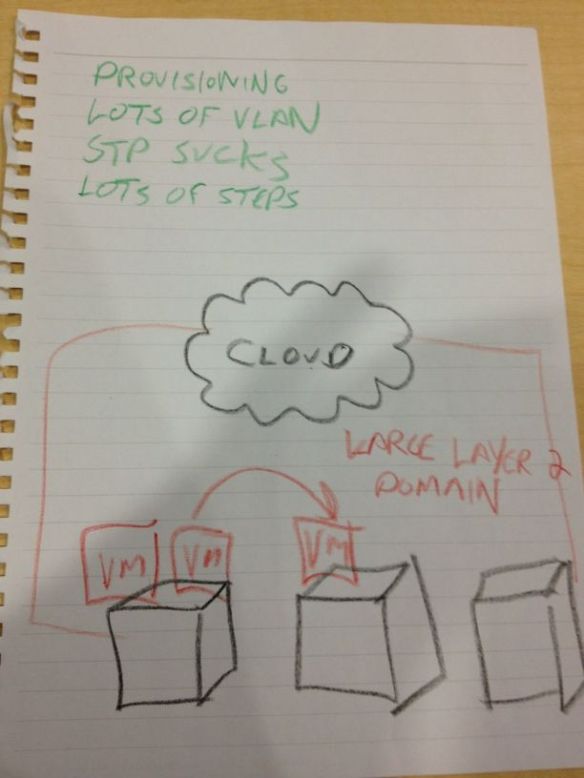
The Problem - courtesy of Tony Bourke
To Juniper’s credit, once I pointed out that we may or may not have seen this slide before, the presenter quickly acknowledged it and moved on quickly to get to the good stuff about QFabric. I didn’t necessarily learn any more about QFabric that I already knew from my own research, but it was a good talk overall. If you want to delve more into QFabric, head over to Ivan’s site and read through his QFabric posts.
Our last treat from the super session was a tour of the Proof-of-Concept labs at the Juniper EBC. They’ve got a lot of equipment in there and boy is it loud! I did get to see how Juniper equipment plays well with others, though, as they had a traded-in CRS-1 floating around with a big “I Wish This Ran Junos” sticker. Tony Mattke was even kind enough to take a picture of it.
Here are the videos: Part 1 – Introduction to Junos
Part 2 – Open Flow Deep Dive
Part 3 – A Dive Into Security
Part 4 – Network Design with QFabric
Tom’s Take
I’m coming around to Juniper. The transaction-based model allows me to fat-finger things and catch them before I screw up royally. Their equipment runs really well from what I’ve been told and their market share seems to be growing in the enterprise from all accounts. I’ve pretty much consigned myself at this point to learning Junos as my second CLI language, and the access that Dan Backman is going to provide to Junosphere will help in that regard. I can’t say how long it will take me to be a convert to the cause of Juniper, but if they ever introduce a phone system into the lineup, watch out! I also consider the fine presentations that were put on in this four hour session to be the benchmark for all future Tech Field Day presenters. Very little fluff, packed with good info and demonstrations is the way to go when you present to delegates at Tech Field Day. Otherwise, the water bottles will start flying.
Tech Field Day Disclaimer
Juniper was a sponsor of Network Field Day 2, as as such was responsible for paying a portion of my travel and lodging fees. They also provided us with breakfast and a USB drive containing the Day One Juniper guides and markting collateral. At no time did Juniper ask for, nor where they promised any kind of consideration in the drafting of this review. The analysis and opinions herein are mine and mine alone.